Companies everywhere are on high alert when it comes to keeping their data secure. However, this doesn’t always mean they follow the best practices when it comes to cybersecurity. According to IBM, 77 percent of IT professionals stated that they do not have a cybersecurity incident response plan. However, there are preventative measures companies can take to stop a data leak from happening.
Educate Your Workforce to Stay Cybersecure
One of the best things you can do to protect your business is to make sure your employees adopt cybersecurity best practices. This includes reporting any possible issues to the IT department, knowing how to identify a phishing email, and only working from company devices. It’s important to make sure these policies are followed company-wide, and are visible and announced to all employees.

You should start educating employees on these policies and procedures during onboarding, and continue training throughout their time with the company. It’s important to note that for this to work, there need to be clear company-wide consequences for not following best practices. Set clear expectations during ethics training so all employees know they are essential to the security of the organization. It only takes one person to allow cyber-criminals access to your network.
Only Use Secure Software
Following cybersecurity best practices is a good start, but it’s not enough on its own. In today’s age, most official business is conducted over the Internet. This includes signing official documents, paying bills, updating medical records and more. This can be safe to do, but only if proper cybersecurity measures are in place.
Using programs that guarantee your company’s data is secure would be the best way to do this, especially when your employees and customers are depending on you to protect their data from cybercriminals.
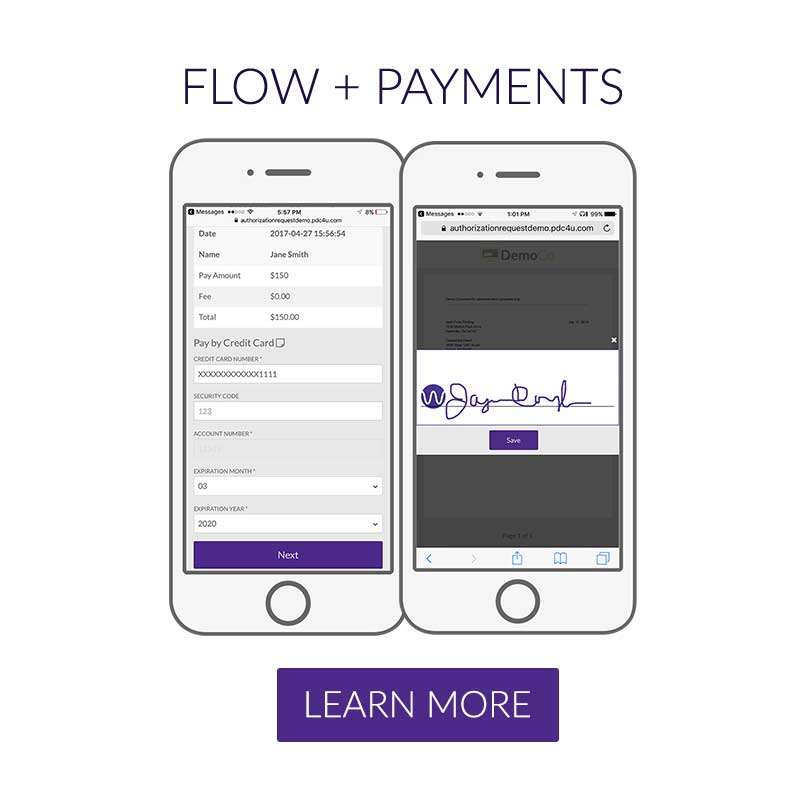
It is critical to use software that has features such as dual-authentication, geo-location and time stamping when securing payments and confidential authorizations from consumers. Software such as PDCflow offers all of these features and more, making FLOW Technology a solid choice.
Protect Your Devices
The final step in cybersecurity is to make sure all your devices are protected. This means using products such as antivirus software to make sure cybercriminals cannot get access to your network or servers. This software will protect you against several different threats, such as adware and ransomware, and alert you if an attack was attempted.
It’s also important to install any and all updates that are recommended on your devices. Updating software means patching bugs and resolving other issues that can cause your network to become compromised.
Keeping customer’s data secure is of utmost importance for modern companies. To ensure data is safe, companies need to have a plan before a cyberattack occurs, and use every tool available to keep cybercriminals out. Following these cybersecurity best practices can help prevent your company from being on the news as the newest data breach incident.
PDCflow’s secure payment and digital communication tools are designed to keep consumer information secure.
- Our Secure Entry Overlay software allows businesses to take payments without ever recording sensitive card data within their systems.
- PDCflow’s tools can reduce PCI scope, saving time and money, and keeping your organization secure.
- Our system for tokenization and encryption of data ensures data remains safe.
- The dual-authentication process used in our FLOW digital communication tool ensures sensitive information and documents are only accessed by the intended party.
For more information on implementing PDCflow to keep your business secure, request a demo.
Request a Demo:
- ABOUT THE AUTHOR -

Hannah Huerta, Marketing Specialist
Hannah Huerta is a Marketing Specialist at PDCflow. She creates content for the accounts receivable and payment industry.




